I Built an Obfuscated Stealth VPN with TrustTunnel
I Fired WireGuard: How I Built an Invisible, Untraceable Home VPN
For the last few years, WireGuard has been my reliable workhorse. It’s fast, the code is clean, and it just works. But it has one glaring weakness that has always bothered me: it’s loud.
WireGuard is incredibly easy to detect. Its packet signature is distinct, and because it usually runs over UDP, aggressive firewalls and Deep Packet Inspection (DPI) tools can spot it from a mile away. If you’re on a restrictive corporate network or a public Wi-Fi that blocks non-standard ports, WireGuard gets crushed instantly.
I didn’t just want encryption; I wanted camouflage.
So, I tore down my old setup and built something new. I replaced my standard VPN with a stealth tunnel that masquerades as regular HTTPS web traffic.
Let me introduce TrustTunnel to you.
The philosophy of this upgrade was simple: If you look like a website, you don’t get blocked.
My new setup uses HTTP/2 for transport. To any network administrator, ISP, or firewall algorithm monitoring my connection, my data doesn’t look like a VPN tunnel. It looks exactly like I’m browsing a standard, secure website.
The packets are indistinguishable from a user scrolling through a tech blog or checking their bank balance. Because the entire world relies on HTTPS (port 443) to function, blocking my VPN would essentially require breaking the internet.
The Stack: Raspberry Pi + Stealth + AdGuard
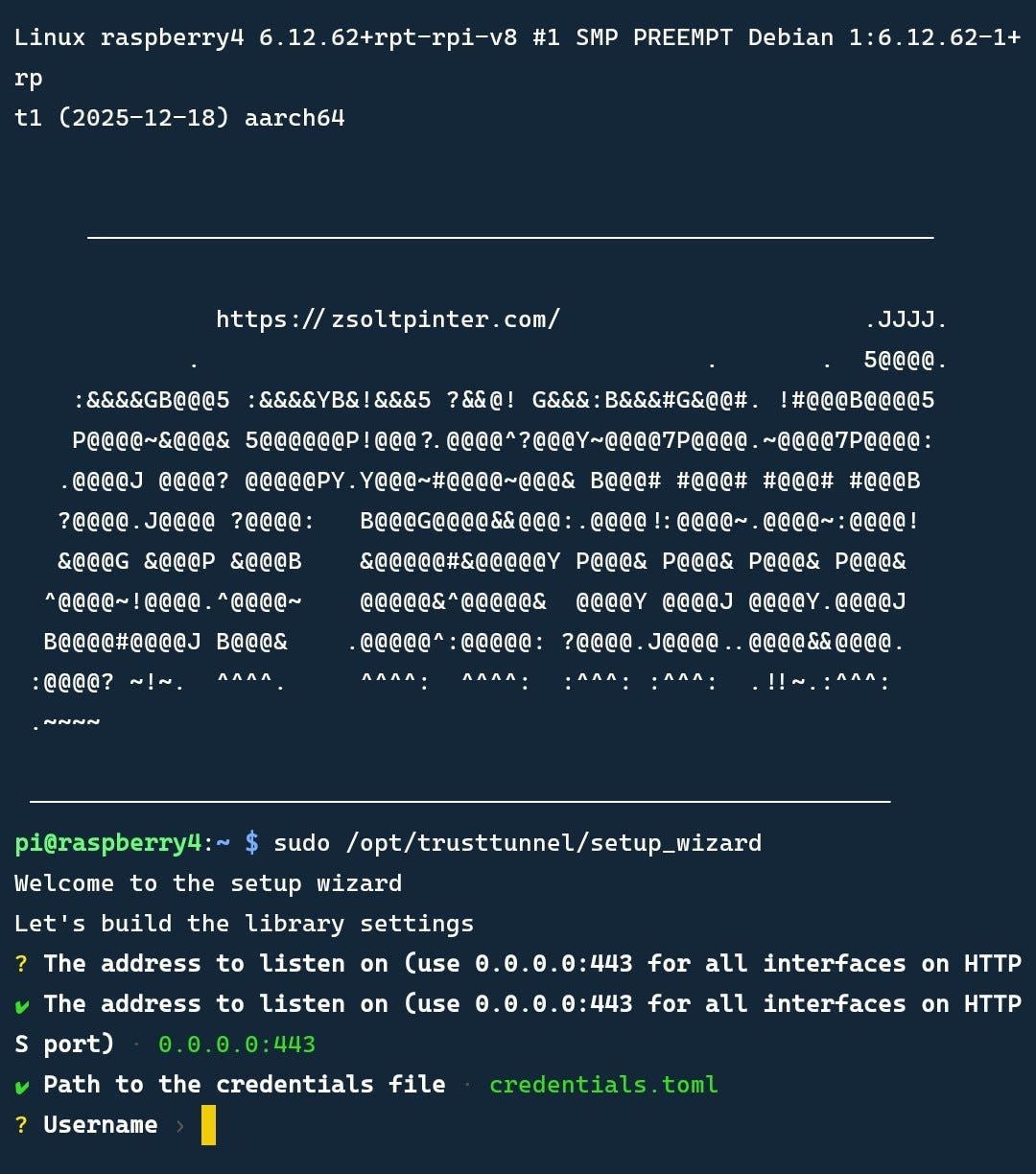
I deployed this on my trusty Raspberry Pi 4, but the software stack is where the magic happens.
1. The Stealth Engine (TrustTunnel)
Instead of the standard UDP handshake of WireGuard, this engine establishes a TLS 1.3 encrypted session. It uses a real, valid SSL certificate (via Let’s Encrypt) and performs a cryptographic handshake that looks identical to loading a webpage.
There is no “pre-shared key” visible in the headers. There is no strange port activity. It is just a silent, persistent stream of HTTPS data.
2. Double-Blind Security
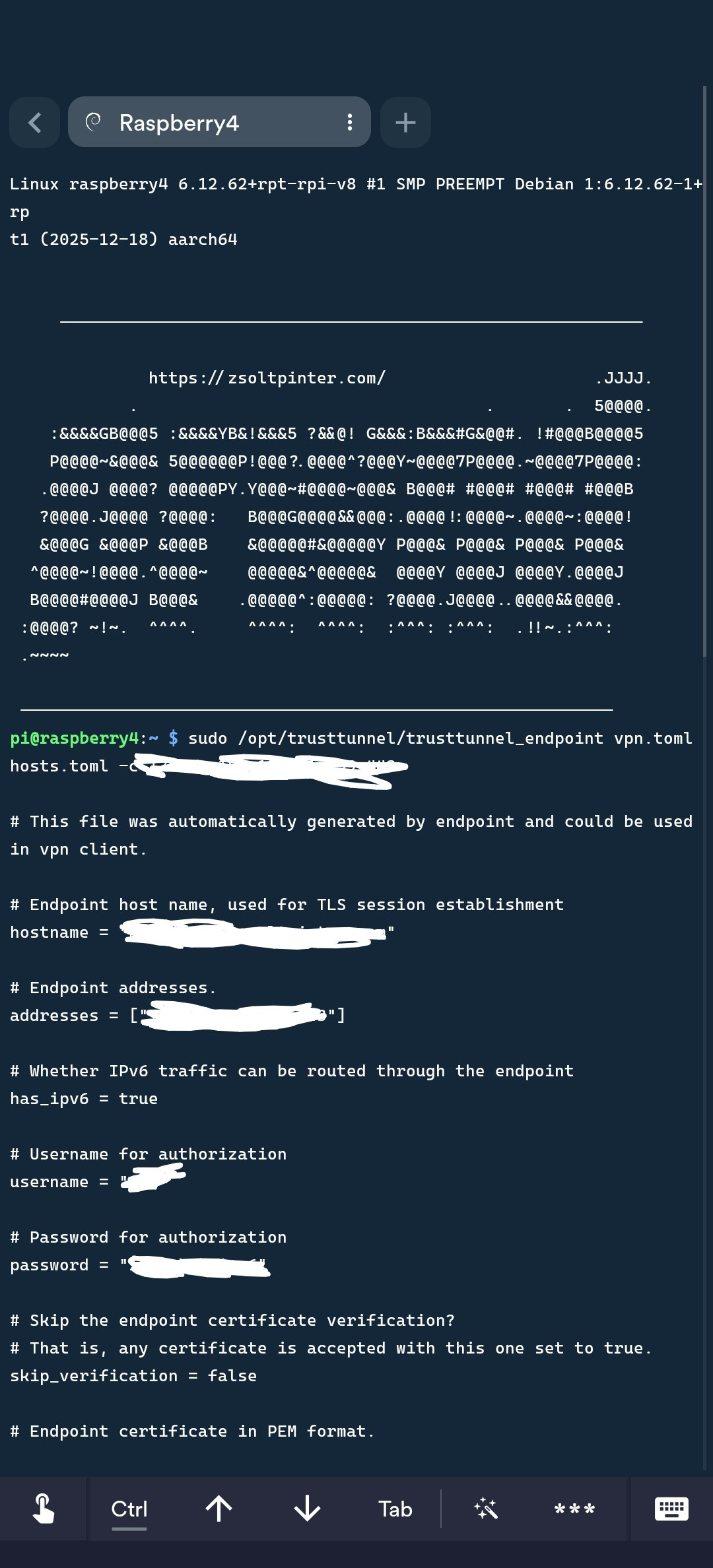
I implemented Certificate Pinning on the client side. This is crucial. My phone doesn’t just trust “any” server; it is hard-coded to trust only the specific cryptographic signature of my Raspberry Pi.
This makes the setup immune to Man-in-the-Middle (MITM) attacks. Even if a sophisticated firewall tries to intercept the connection by presenting a fake certificate (a common technique in restrictive environments), my client immediately drops the packets.
3. The AdGuard Home Integration
Since I was already routing my traffic home, I decided to clean it up. I configured the VPN to pipe all DNS requests directly into a local instance of AdGuard Home running on the same Pi.
The result?
* My phone connects to the Pi via the stealth tunnel.
* The Pi scrubs all ads, trackers, and analytics at the DNS level.
* Clean, encrypted traffic goes out to the internet.
I am not just invisible; I am browsing faster because I’m not downloading megabytes of ad trash.
The “Dynamic” Challenge
One hurdle was my home internet’s Dynamic IP. Hardcoding an IP address in a configuration file is a recipe for disaster—it works until your ISP decides to rotate your lease.
I solved this by setting up a Dynamic DNS (DDNS) script that automatically …
Unfortunately the server IP must be in X.X.X.X format for IPv4. To overcome this limitation I have set up Cloudflared Tunnel so after the rare event of public IP change I always can SSH in remotely to update the config.
The Verdict
WireGuard is great for speed, but this new setup is built for resilience.
Now, when I connect from a draconian coffee shop network or a restricted hotel Wi-Fi, I don’t cross my fingers and hope the UDP ports are open. I just connect. The network sees HTTPS, I see the open internet, and nobody is the wiser.
Digital freedom isn’t just about encryption anymore; it’s about blending in. And right now, my traffic is the best-dressed ghost in the machine. 👻
It works so far… But the real exam is coming up this year.
I’m planning for a trip to a certain "East Asian region" known for having one of the world's strictest internet attendance policy. If you see me online regularly, you’ll know the Ghost Protocol was a success. 💪
If not... well, send dumplings… 🥟🥢